Network performance monitor (npm) as. Rogue aps can be detected by logging into your router as a system administrator. There are a couple of ways of detecting rogue aps. Those should find both an open and closed port on most waps, which improves os detection accuracy. What makes a rogue access point rogue? You can configure your wireless firebox to detect rogue wireless access points that operate in the same range as your wireless network. First i’ll use ifconfig to identify the alfa wnic: Loginask is here to help you access rogue access point detected quickly and. Choose wireless > rogue ap. Rogue access point detected will sometimes glitch and take you a long time to try different solutions.
Beaconing, or requesting a beacon, and network sniffing, or looking for packets in the air. What makes a rogue access point rogue? Rogue wireless access points can present some serious problems for your network. Rogue access point detected will sometimes glitch and take you a long time to try different solutions. Those should find both an open and closed port on most waps, which improves os detection accuracy. How to spot rogue access points a rule of thumb. You can configure your wireless firebox to detect rogue wireless access points that operate in the same range as your wireless network. Cisco meraki defines a rogue access point as an ap that is both “seen” on the lan and is broadcasting ssids that are visible to the. There are two basic approaches for locating rogue access points: There are a couple of ways of detecting rogue aps.
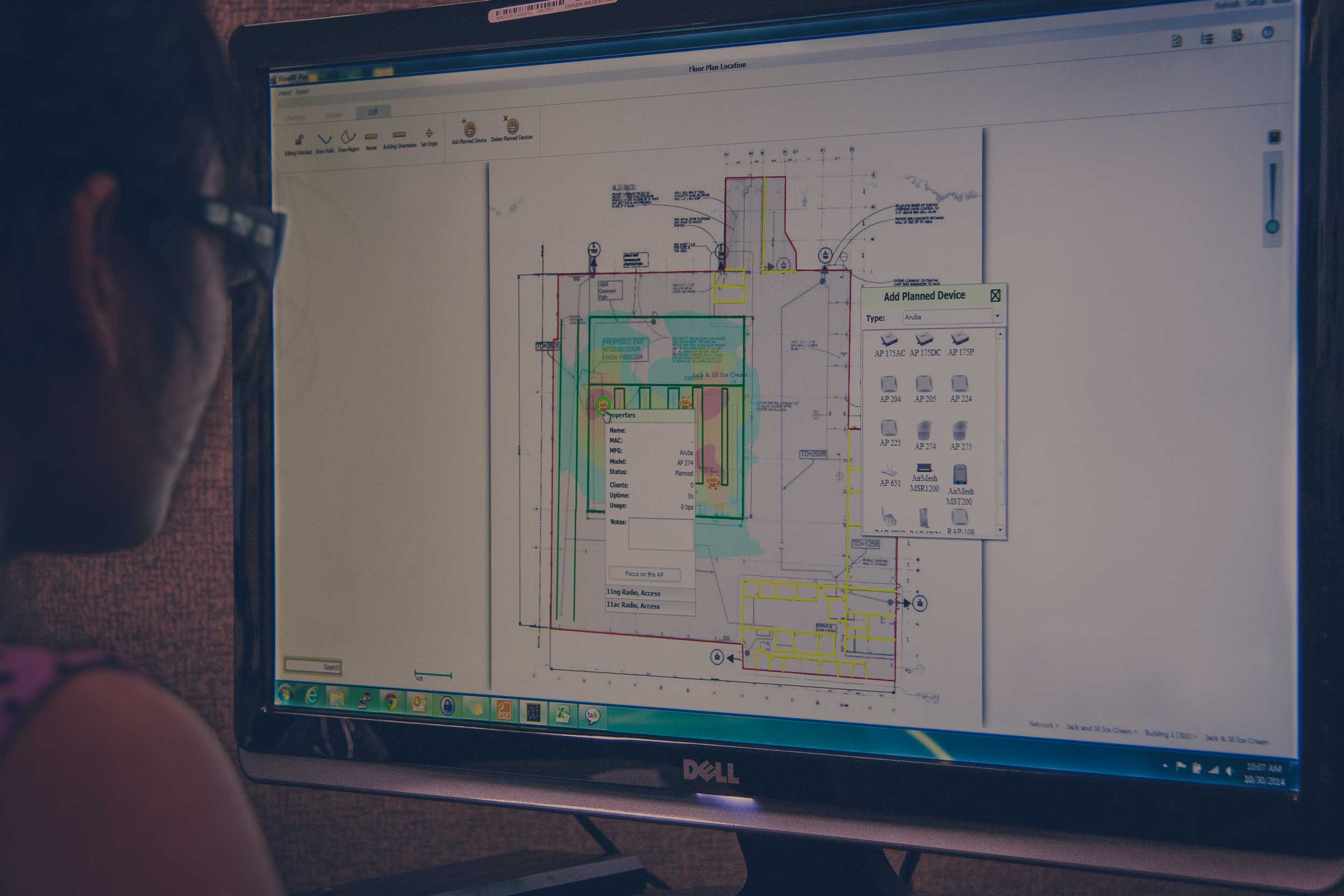
In rogue ap detected table, check the box for the access. There are two basic approaches for locating rogue access points: This will show you all of the access points on the network, and if you see something that has not been. Monitor thin and thick aps and their clients. The first part is just three commands to launch the tool. To authorize detected access points: What makes a rogue access point rogue? Rogue aps can be detected by logging into your router as a system administrator. This hardware solution uses a system of access points to act as a listening network designed to detect new, rogue access points on the network. First i’ll use ifconfig to identify the alfa wnic:
There are two basic approaches for locating rogue access points: In the past, i’ve recommended using netstumbler to identify wireless access points. In rogue ap detected table, check the box for the access. Network performance monitor (npm) as. Rogue wireless access points can present some serious problems for your network. Those should find both an open and closed port on most waps, which improves os detection accuracy. You can configure your wireless firebox to detect rogue wireless access points that operate in the same range as your wireless network. On top of that, the hacker can take advantage of the rogue access points to launch ddos attacks to kick you out of the network. Click the rogue ap detection on radio button. Monitor thin and thick aps and their clients.
On top of that, the hacker can take advantage of the rogue access points to launch ddos attacks to kick you out of the network. A rogue access point is any wireless access point. Network performance monitor (npm) as. What makes a rogue access point rogue? Rogue access point detected will sometimes glitch and take you a long time to try different solutions. There are a couple of ways of detecting rogue aps. Rogue wireless access points can present some serious problems for your network. Cisco meraki defines a rogue access point as an ap that is both “seen” on the lan and is broadcasting ssids that are visible to the. Click the rogue ap detection on radio button. There it is, ready to get started.